At Bank of Jerusalem, we are committed to protecting your financial and personal data with the most advanced technologies, ensuring that you can enjoy our full variety of online banking service with complete peace of mind.
How do we protect your information?
- Strong Identity Verification – When attempting to access the system, your identify is verified through a username and password or an OTP (one-time password), which is sent to your mobile phone via text message
- Database Protection – All databases are protected by state-of-the-art cybersecurity systems.
- Data Encryption – All data sent from your PC to the Bank's computers, and vice versa, is encrypted to prevent eavesdropping (man-in-the-middle attacks) by unauthorized partes
- Continuous Security – Bank of Jerusalem's website is monitored 24/7 by expert security teams, who are able to identify and prevent unauthorized account intrusion attempts
- Stringent Cybersecurity Checks – The website is regularly tested by internal and external information security professionals
- Automatic Logoff – You will be automatically logged off from your account if the system detects that you have been inactive for a period of time. This prevents your account from being accessed by an unauthorized person
Secure Account Access
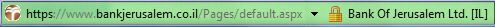
When visiting the Bank of Jerusalem website and accessing your personal account, you will see a closed padlock icon in the address bar – indicating that all communication with the website is secure – as well as the letters https at the beginning of the address bar. You can double-click the padlock icon to open a digital certificate, confirming that the current website does indeed belong to Bank of Jerusalem.
![]() Finished using the wide range of services offered on the Bank of Jerusalem site? Make sure you always log off from the service by clicking the "Exit" button, located above the toolbar at the top of the page.
Finished using the wide range of services offered on the Bank of Jerusalem site? Make sure you always log off from the service by clicking the "Exit" button, located above the toolbar at the top of the page.
Several key details should be checked in order to verify that the service is secure and that you are on the real, legitimate Bank of Jerusalem website rather than a spoof or impostor website:
1
A spoof site will look like the regular Bank of Jerusalem site, but the URL displayed in the address bar will be different, and may not contain the https prefix, which indicates secure communication.
2
When visiting the Bank of Jerusalem website, always immediately check that you are on the correct site before performing any transactions in your personal account. The
correct URL is:
https://services.bankjerusalem.co.il/
3
In order to ensure that you are always using the official Bank of Jerusalem website rather than a spoof site, avoid accessing the website via links or emails from an unfamiliar source.
4
For your convenience, the Bank of Jerusalem website always displays the date and time of your last visit. This means that you can easily check whether anyone has accessed your account without your knowledge.
Additional areas in information security

Passwords
Passwords are a very important tool for safeguarding your accounts, devices, and data from unauthorized access.
Phishing
Phishing is an attempt by malicious parties to exploit human weaknesses in order to obtain sensitive personal information
Protecting Your PC & Phone
We recommend installing and regularly updating the security systems for your PC such as Antivirus software, Firewall and more
Customer Activity Records in the Bank's Computer Systems
Please be aware that Bank of Jerusalem records all customer transactions and instructions, including their content and date.
If you suspect unauthorized use of your account or the theft of information used to verify your identity for the website, loss or theft of a mobile phone, misuse of a mobile phone, or a change in your phone number, notify the Bank immediately in the way that is most convenient for you:
-
Contact a Bank of Jerusalem Representative
*5727
-
Contact the Technical Support Center










